STACC
Stopping Microarchitectural Attacks through Constant-time Code
While computing devices control and monitor increasingly many areas of our life, the security of these devices remains an open issue. The recent disclosure of Meltdown, Spectre and now Foreshadow showcased the remaining vulnerability of the microarchitecture of modern CPUs - highlighting the relevance of microarchitectural attacks to our computing infrastructure. Decades-long optimization for performance have created CPUs where any knowledgeable adversary who can execute code will easily overcome logic separation between processes and thus compromise system security. To ensure the expected reliability and longevity of the computing infrastructure, mitigation of microarchitectural attacks is of utmost importance.
This project addresses microarchitectural attacks with two complementary approaches:
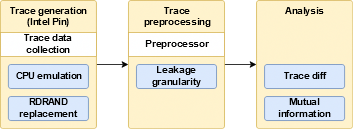
- Detect vulnerabilities in hardware and code. We develop a framework (Microwalk) to quantify information leakage caused by microarchitectural features on modern computing platforms. Through the combination of static analysis for Spectre-like attacks with a novel fuzzer-based dynamic analysis approach for reliable yet scalable leakage detection, we can detect vulnerability for binary code of any size.
- Prevent attacks through better development tools. We integrate our tools directly into the compiler toolchain, easing the generation of invulnerable programs even for developers who are not familiar with side-channel resistant programming techniques.
This project is funded by Deutsche Forschungsgemeinschaft (DFG).